SSO Module 1 - CyberSecurity 101: From Viruses to the Hacker Spectrum
Dive into digital safety: from decoding computer viruses to navigating the hacker spectrum. Equip with defenses for our interconnected age. Discover from White Hat to Black Hat. Fortify with CyberSecurity 101. Join the Web3 network today!
Welcome to the frontier of digital safety! In this age where everything is interconnected, the vast realm of the internet holds both wonders and threats. Dive in to unravel the mysteries of computer viruses, understand their cunning nature, and equip yourself with powerful countermeasures. Additionally, familiarize yourself with the enigmatic world of hackers - the good, the bad, and the grey. Whether you're a seasoned tech-savvy individual or someone just beginning to navigate the digital cosmos, this guide promises invaluable insights. Embark on this journey to fortify your defenses and ensure your online adventures remain safe and enjoyable. Let's get started!
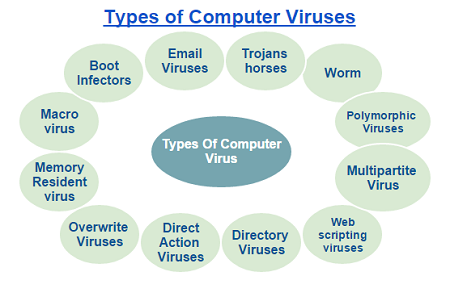
1. Understanding Computer Viruses
Computer viruses are malicious codes integrated into legitimate software, which replicate and infect other programs, causing disruptions and potential damage. Here, we explore various virus categories and preventive measures.
File Virus:This virus latches onto files and modifies their initial sequence to execute its code, acting parasitically.
Preventive Measures:
- Keep your antivirus software up-to-date.
- Be cautious with email attachments from unverified sources.
- Avoid unfamiliar software downloads.
Boot Sector Virus:Targeting the boot sector of disks or the master boot record (MBR), this virus executes upon system boot-up, spreading via floppy disks.
Preventive Measures:
- Regularly update antivirus software.
- Be wary of potentially contaminated disks.
- Utilize disk protection utilities.
Macro Virus:Residing within document macros, these activate upon document access, leading to potential system-wide infections.
Preventive Measures:
- Employ macro defense tools.
- Regularly update antivirus applications.
- Avoid opening unverified documents.
Source code Virus:This variant seeks and alters source code to propagate itself.
Preventive Measures:
- Ensure antivirus protection.
- Implement code review processes.
- Utilize source code management platforms.
Polymorphic Virus:Eluding antivirus detection, these viruses alter their digital signatures upon each installation.
Preventive Measures:
- Utilize sophisticated antivirus solutions.
- Update all software and OS routinely.
Encrypted Virus:To dodge detection, this virus is encrypted, bringing along a decryption mechanism for execution.
Preventive Measures:
- Opt for advanced antivirus solutions.
- Stay vigilant with email attachments and unfamiliar software downloads.
Stealth Virus:This cunning virus evades antivirus detection by mimicking uninfected files or altering its location.
Preventive Measures:
- Invest in top-tier antivirus technology.
- Update systems and software.
- Exercise caution when downloading or accessing unfamiliar content.
Tunneling Virus:Designed to disable interception programs, these viruses embed within interrupt handler chains or device drivers.
Preventive Measures:
- Choose advanced antivirus applications.
- Regularly update software and OS.
- Avoid unknown software and email attachments.
Multipartite Virus:Infecting various system components, its multifaceted nature complicates detection.
Preventive Measures:
- Use cutting-edge antivirus software.
- Conduct full system scans routinely.
- Ensure timely system and software updates.
Armored Virus:Equipped to counteract antivirus measures, these viruses employ tactics to confuse or misdirect antivirus solutions.
Preventive Measures:
- Adopt advanced antivirus solutions.
- Refrain from downloading or accessing suspicious content.
- Stay updated with the latest system enhancements.
Browser Hijacker:Targeting browsers, it modifies settings or redirects users to harmful web pages.
- Preventive Measures:
- Use specialized antivirus tools for browsers.
- Regularly update browser versions.
- Be selective with browser extensions and their sources.
Memory Resident Virus:These embed in your RAM, often discreetly attaching to antivirus files.
Preventive Measures:
- Opt for sophisticated antivirus tools.
- Reboot your device regularly.
- Update your system consistently.
Direct Action Virus:This virus attaches to executable files and remains concealed in memory. It's also known as a Non-Resident Virus.
Preventive Measures:
- Employ antivirus solutions.
- Be cautious with unfamiliar files.
- Keep software and systems updated.
Overwrite Virus:Destroys the content of its infected files, making them unusable.
Preventive Measures:
- Implement antivirus software.
- Exercise caution with unknown files.
- Always back up data.
Directory Virus:Modifies directory paths, also known as File System or Cluster Virus.
Preventive Measures:
- Utilize advanced antivirus tools.
- Regularly update software.
- Conduct thorough system scans.
Companion Virus:Mimics legitimate files by replicating filenames but changes the extension.
Preventive Measures:
- Rely on antivirus software.
- Be mindful of file origins.
- Scrutinize file extensions closely.
FAT Virus:Targets the File Allocation Table (FAT), crucial for data access on certain computer systems. An attack can result in extensive system damage.
Preventive Measures:
- Use high-quality antivirus tools.
- Steer clear of suspicious files or links.
- Frequently back up data and maintain software updates.
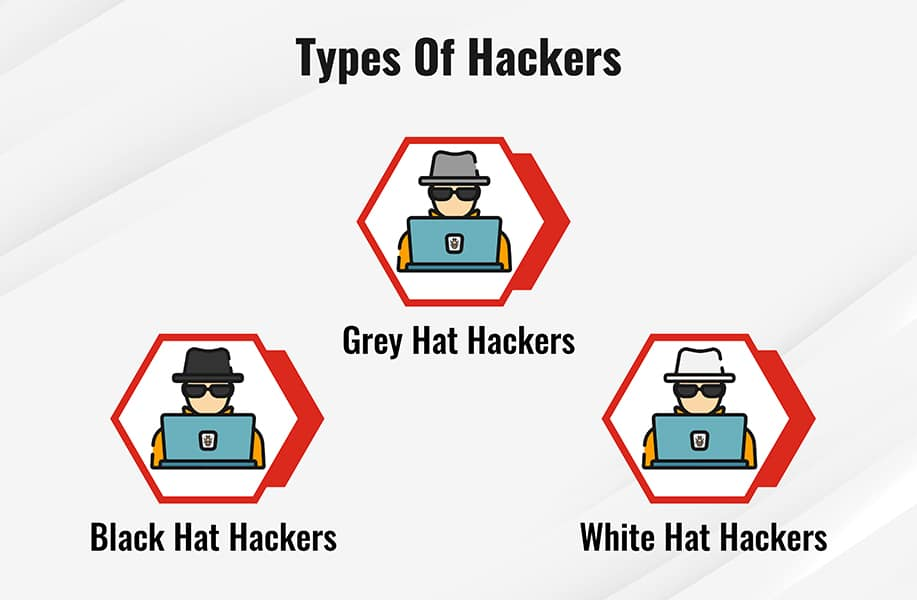
Types of Hackers:
White Hat Hackers:Ethical hackers trained to locate and rectify vulnerabilities in systems, aiding in fortifying cyber defenses.
Grey Hat Hackers:Operate in the gray zone, identifying system vulnerabilities without explicit permission. Though not malicious, their actions aren't always legal.
Black Hat Hackers:Malicious individuals who exploit system vulnerabilities for personal gains, often leading to data theft or system damage.
To Protect Against Hackers:
- Consistently update software.
- Employ antivirus tools.
- Activate two-factor authentication.
- Stay informed about the latest threats.
- Backup essential data regularly.
- Avoid clicking on suspicious emails or links.
- Use robust and unique passwords.
- Secure your Wi-Fi and change default settings.
- Follow cybersecurity experts for updates.
- Consult professionals for cybersecurity concerns.
Summary
Congratulations! You finished Module 1: CyberSecurity 101: From Viruses to the Hacker Spectrum
Let’s review your learnings:
Types of Viruses:
- File Virus - Modifies files to execute malicious code.
- Boot Sector Virus - Targets boot sector or MBR for execution.
- Macro Virus - Activates within document macros.
- Source code Virus - Seeks and alters source code to propagate.
- Polymorphic Virus - Alters its digital signatures to evade detection.
- Encrypted Virus - Uses encryption to dodge antivirus detection.
- Stealth Virus - Mimics uninfected files or changes its location to avoid detection.
- Tunneling Virus - Embeds in device drivers or interrupt handler chains.
- Multipartite Virus - Infects multiple system components, complicating detection.
- Armored Virus - Employs tactics to counteract antivirus detection.
- Browser Hijacker - Modifies browser settings or redirects users.
- Memory Resident Virus - Embeds in RAM, sometimes targeting antivirus files.
- Direct Action Virus - Attaches to executable files and stays concealed.
- Overwrite Virus - Destroys content of infected files.
- Directory Virus - Alters directory paths.
- Companion Virus - Mimics legitimate files by changing extensions.
- FAT Virus - Targets the File Allocation Table, risking extensive system damage.
Types of Hackers:
- White Hat Hackers - Ethical hackers enhancing cyber defenses.
- Grey Hat Hackers - Identify vulnerabilities without permission; operate in a moral gray zone.
- Black Hat Hackers - Malicious actors exploiting systems for personal gain.
So, do you want to keep learning? Look at the full course here and join the conversation on Discord to start building your network in the Web3 space today!
This article was brought to you by:


